吃燒餅沒有不掉芝麻的,而開網站的沒有不被攻擊的… 奇怪了,世界上還真多無聊人士,吃飽就想如何攻擊別人的網站,不知道是什麼心態. 一種常見的攻擊是貼廣告或是莫名其妙的留言,這些都是要廣告特定的 URL,這種攻擊在 WordPress 的網站用 Spam Karma 就可以有效對付;另有一種刻意要癱瘓網站的攻擊,常見的作法就是發動很多很多的用戶端要求,持續讓網站窮於應付,用掉資源(CPU的資源,socket的資源,頻寬的資源…),而使得網站無法服務正常的使用者,這就是所謂的 DoS — Denial of Service 攻擊,我翻譯為阻絕服務攻擊。
本格平常好好的經營,也沒作什麼壞事,但卻碰過好幾次 DoS 攻擊,IP 的來源是中國及俄羅斯 🙂 . 針對 DoS 攻擊,官方的 Apache 本身並沒有提供解決之道,現在找到的是一個 3rd party 的模組,mod_evasive,用以下原理防治: Detection is performed by creating an internal dynamic hash table of IP Addresses and URIs, and denying any single IP address from any of the following:
- Requesting the same page more than a few times per second
- Making more than n concurrent requests on the same child per second
- Making any requests while temporarily blacklisted (on a blocking list)
它的 README 寫對付 DDoS — Distributed DoS 也有效,可是由這幾點看不出來如何有效。
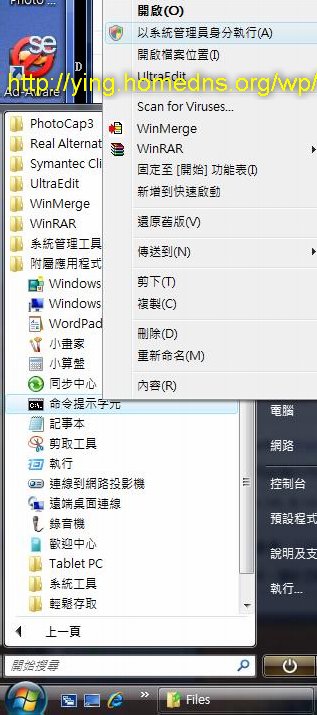
由於的使用的是在 Vista (Win32)上的 Apache,要把上面的程式 compile 出來也是很麻煩,幸好在 這裡 有 mod_dosevasive Win32 binary for Apache 2.2,可以找到一個叫 dosevasive.zip 的檔案。
用法也蠻簡單的,先載入模組,在 httpd.conf 加入
LoadModule dosevasive22_module modules/mod_dosevasive22.dll
就好了,參數都有預設值,如果要微調,在 httpd.conf 加入:
DOSHashTableSize 3097
DOSPageCount 2
DOSSiteCount 50
DOSPageInterval 1
DOSSiteInterval 1
DOSBlockingPeriod 10
再作各參數微調,請自己看看以下說明,就不逐條翻譯了。
DOSHashTableSize
—————-
The hash table size defines the number of top-level nodes for each child’s
hash table. Increasing this number will provide faster performance by
decreasing the number of iterations required to get to the record, but
consume more memory for table space. You should increase this if you have
a busy web server. The value you specify will automatically be tiered up to
the next prime number in the primes list (see mod_evasive.c for a list
of primes used).
DOSPageCount
————
This is the threshhold for the number of requests for the same page (or URI)
per page interval. Once the threshhold for that interval has been exceeded,
the IP address of the client will be added to the blocking list.
DOSSiteCount
————
This is the threshhold for the total number of requests for any object by
the same client on the same listener per site interval. Once the threshhold
for that interval has been exceeded, the IP address of the client will be added
to the blocking list.
DOSPageInterval
—————
The interval for the page count threshhold; defaults to 1 second intervals.
DOSSiteInterval
—————
The interval for the site count threshhold; defaults to 1 second intervals.
DOSBlockingPeriod
—————–
The blocking period is the amount of time (in seconds) that a client will be
blocked for if they are added to the blocking list. During this time, all
subsequent requests from the client will result in a 403 (Forbidden) and
the timer being reset (e.g. another 10 seconds). Since the timer is reset
for every subsequent request, it is not necessary to have a long blocking
period; in the event of a DoS attack, this timer will keep getting reset.
WHITELISTING IP ADDRESSES
IP addresses of trusted clients can be whitelisted to insure they are never
denied. The purpose of whitelisting is to protect software, scripts, local
searchbots, or other automated tools from being denied for requesting large
amounts of data from the server. Whitelisting should *not* be used to add
customer lists or anything of the sort, as this will open the server to abuse.
This module is very difficult to trigger without performing some type of
malicious attack, and for that reason it is more appropriate to allow the
module to decide on its own whether or not an individual customer should be
blocked.
To whitelist an address (or range) add an entry to the Apache configuration
in the following fashion:
DOSWhitelist 127.0.0.1
DOSWhitelist 127.0.0.*
Wildcards can be used on up to the last 3 octets if necessary. Multiple
DOSWhitelist commands may be used in the configuration.
下载dosevasive.zip的页面已经无法打开,不知道您这里时候还有dosevasive.zip的文件?如果有能否发一份给我,不胜感激!
還在,仔細找找。
你好呀 本人在網絡上 search 到你關於 apache ddos 的文章
本人現在的Windows server 2008 R2 行 Apache 2.4
發覺 httped.exe 入面 Send(B/Sec) 非常之大 其實是佔100%了
請問一下 知不知道 有沒有方法解決?
圖片在我的討論區內 不好意思 也不到網空放圖,所以放到我自已的web server 內
http://www.hkcsteam.com/viewthread.php?tid=980&extra=page%3D1
如果有解決方法 能否電郵通知一下我 elitecllau@gmail.com